Videos, specifically .MP4s, are probably the largest files on your file servers. In part, this is due to the explosion of cheap cameras that record very high definition video. The latest iPhone can record video at 4K yetI have some projectors that can’t show a resolution greater than 720p! Talk about a waste of space.
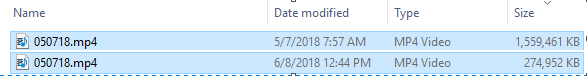
So, what is a server admin to do? The same thing we did to pictures, shrink some files with PowerShell! Below, you will see a screenshot of the same video before and after conversion!
The script will:
- automatically go through a network share that is used for folder redirection / home folders.
- Convert MP4 files to a 720p resolution. If you want a higher or lower resolution, edit line 255 by changing the preset value.
- Remove the old file if it is larger than the new file.
- Reset all ownership and permissions
- Tag the file so that future conversions run faster.